ReHacked vol 248: Strange underground city found in man's basement, Open Source Liability is Coming, Europol warns 443 online shops infected with credit card stealers and more
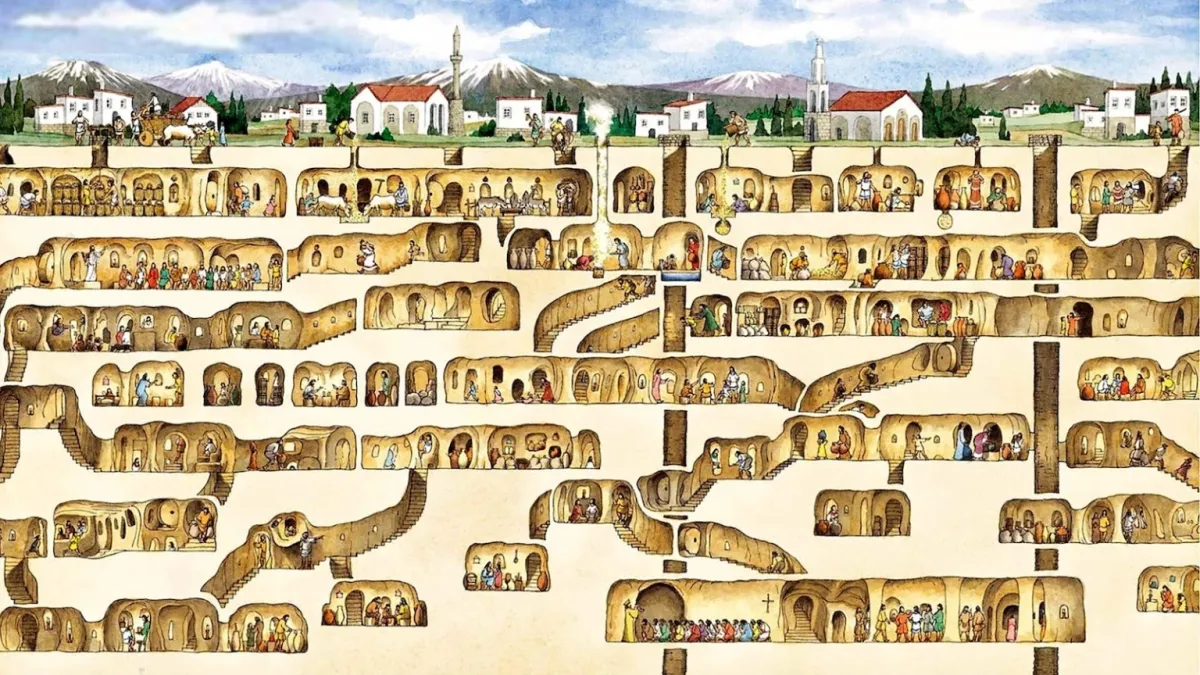
Derinkuyu: Strange underground city found in man's basement - Big Think #history
In 1963, a man knocked down a wall in his basement and discovered a mysterious underground city. The subterranean city is up to 18 stories and 280 feet deep in places and probably thousands of years old. The Derinkuyu Underground City is the largest of its kind: It could house 20,000 people.
Make a donation - support Ukraine
Urgent Action Fund for Women’s Human Rights | Supporting women and LGBTQI+ people in and around Ukraine
Voices of Children | Helping children in Ukraine affected by conflict
Support the Armed Forces of Ukraine | via National Bank of Ukraine
Don’t forget to share if you like what you read here, subscribe (if not yet) and leave a comment. Any form of your feedback is very important to me. Thanks!
RSS feed available if you don’t want to clutter your inbox.
The X220 ThinkPad is the Best Laptop in the World https://bt.ht/posts/x220/ #hardware
The X220 ThinkPad is the greatest laptop ever made and you're wrong if you think otherwise. No laptop hardware has since surpassed the nearly perfect build of the X220. New devices continue to get thinner and more fragile. Useful ports are constantly discarded for the sake of "design". Functionality is no longer important to manufacturers. Repairability is purposefully removed to prevent users from truly "owing" their hardware.
EU CRA: What does it mean for open source? - Bert Hubert's writings #copyrights
I mentioned Google’s libwebp earlier, and how Google is not on the hook directly for that library since they don’t monetize it. However, Google Chrome relies on libwebp, which means Google should perform due diligence on it, because Chrome is most certainly monetized.
In this way, it is fair to say that the EU CRA does not apply directly to most open source. But it does apply to all commercial open source users. And in this boomerang way, most open source software will receive CRA scrutiny, where the costs will be born by the users, and not the developers. This seems to me a good thing.
What comes after open source? Bruce Perens is working on it • The Register #copyrights
"First of all, our licenses aren't working anymore," he said. "We've had enough time that businesses have found all of the loopholes and thus we need to do something new. The GPL is not acting the way the GPL should have done when one-third of all paid-for Linux systems are sold with a GPL circumvention. That's RHEL."

#software
Open Source Liability is Coming | Developers Alliance #software #copyrights
EU policymakers are clear; going forward, someone must be liable for software harm. Data was lost, customers couldn’t transact, files got garbled, hackers made entries – someone in the software chain must make the user whole. Today you can license-away that liability by putting the onus on the user to accept the risk, since bugs happen and hackers hack. Not your fault, you did your best, and you told the user that upfront. My read of the emerging regime changes that. It forces you to prove your code wasn’t the cause of the harm – “strict liability” in legal circles. Products like cars often get regulated this way. Essentially, the carmaker is at fault when something goes wrong unless they can prove they’re not. It’s a way of shifting societal costs back to the party that profits from the product in question. It allows consumers to be confident that cars are safe, without having an expert reverse engineer them before use or agreeing to accept that the brakes may fail – too bad for you. The carmaker designed and built a complex thing so they should be in the best position to prove they implemented appropriate safeguards.
Europol warns 443 online shops infected with credit card stealers #security
Europol has notified over 400 websites that their online shops have been hacked with malicious scripts that steal debit and credit cards from customers making purchases.
Skimmers are small snippets of JavaScript code added to checkout pages or loaded from a remote resource to evade detection. They are designed to intercept and steal payment card numbers, expiration dates, verification numbers, names, and shipping addresses and then upload the information to the attackers' servers.
Foundations — Greg Egan #science #history #physics #nature
Foundations is a series of articles, first published in the magazine Eidolon, on some of the theories of twentieth-century physics that have most influenced modern science fiction. However, these are not essays on the history or philosophy of science; their aim is to show how the central idea of each theory leads to detailed, quantitative predictions of real physical effects. For example, the article on special relativity derives formulas for time dilation, Doppler shift, and aberration.
These articles are for the interested lay reader. No prior knowledge of mathematics beyond high school algebra and geometry is needed.
4-year campaign backdoored iPhones using possibly the most advanced exploit ever | Ars Technica #security
Researchers on Wednesday presented intriguing new findings surrounding an attack that over four years backdoored dozens if not thousands of iPhones, many of which belonged to employees of Moscow-based security firm Kaspersky. Chief among the discoveries: the unknown attackers were able to achieve an unprecedented level of access by exploiting a vulnerability in an undocumented hardware feature that few if anyone outside of Apple and chip suppliers such as ARM Holdings knew of.
“The exploit's sophistication and the feature's obscurity suggest the attackers had advanced technical capabilities,” Kaspersky researcher Boris Larin wrote in an email. “Our analysis hasn't revealed how they became aware of this feature, but we're exploring all possibilities, including accidental disclosure in past firmware or source code releases. They may also have stumbled upon it through hardware reverse engineering.”
Donald Knuth's 2023 Christmas Lecture: Making the Cells Dance - The New Stack #interesting
Beginning programmers are taught about linked lists — where every element in the list contains not only a value, but also the location for the next and previous elements. Knuth helped popularize a way of moving through those elements where “it just seems that these numbers in the computer are following an elegantly-choreographed dance, and so that’s why I call it dancing links.” Knuth discussed them in 2018, and this year’s lecture was described as a kind of sequel.
“We’ve improved dancing links now to something that has the jazzy name dancing cells.”
The New York Times sues OpenAI and Microsoft for copyright infringement - The Verge #copyrights
The New York Times is suing OpenAI and Microsoft over claims the companies built their AI models by “copying and using millions” of the publication’s articles and now “directly compete” with the outlet’s content.
As outlined in the lawsuit, the Times alleges OpenAI and Microsoft’s large language models (LLMs), which power ChatGPT and Copilot, “can generate output that recites Times content verbatim, closely summarizes it, and mimics its expressive style.” This “undermine[s] and damage[s]” the Times’ relationship with readers, the outlet alleges, while also depriving it of “subscription, licensing, advertising, and affiliate revenue.”
A Man Hiding from the Nazis Made 95 Issues of a Highly Creative Zine (1943-1945) | Open Culture #history
Bloch not only produced an impressive 95 issues between August 1943 and April 1945, he did so as a German Jew hiding from the Nazis in the rafters of a private home in the Dutch city of Enschede, not far from the German border.
His cut-and-paste illustrations are part of a long-standing zine continuum, made possible in part by helpers who furnished him with pens, glue, newspapers and other collage-worthy materials, in addition to food and other necessities.
If you would like to propose any interesting article for the next ReHacked issue, just hit reply or push this sexy “Leave a comment” (if not subscribed yet) button below. It’s a nice way to start a discussion.
Thanks for reading this digest and remember: we can make it better together, just leave your opinion or suggestions after pressing this button above or simply hit the reply in your e-mail and don’t forget - sharing is caring ;) Have a great week!
Dainius